1. INTRODUCTION
2. BACKGROUND
2.1. Open Source Ground Stations
2.2. RF Attacks
3. THREAT MODEL
3.1. Attack Model
3.2. Attack Scenario
4. METHODOLOGY
4.1. Jamming
4.2. Replay Attack
5. EXPERIMENT
5.1. Environment
5.2. Result
6. CONCLUSION
1. INTRODUCTION
In recent years, the space industry has experienced significant growth. This expansion is highlighted by an increasing number of satellite launches [1] and the rise of the New Space era [2]. This shift, driven by private sectors, such as SpaceX, has greatly reduced the cost and complexity of developing space vehicles, enabling rapid industrial expansion. At the same time, technologies that were once classified as national secrets are now available as open sources. For example, NASA has released the Core Flight System [3] as an open source, while several CubeSat platforms [4,5] have also made their software and hardware publicly available. These developments have lowered technical barriers, encouraged innovation, and facilitated broader participation by independent researchers and academic institutions.
Open-source technologies have also made significant advances in ground stations, playing a critical role in facilitating communication between space systems and ground segments. Projects such as SatNOGS [6] and TinyGS [7] represent this movement, allowing users to build personal ground stations using low-cost hardware and easy installation procedures. The necessary software can be easily installed on compatible boards, making the systems highly accessible to non-experts. As a result, the number of open-source ground stations has increased significantly, creating a globally distributed network. This development has improved access to satellite data and has encouraged further collaboration within the space technology community.
While open-source ground stations offer significant advantages, they may be particularly vulnerable to cyberattacks. First, the public availability of software code provides attackers with extensive information that can be exploited for malicious purposes. In addition, because most open-source ground stations are operated by individuals, security practices are often inadequate compared to professionally managed infrastructure. This problem is exacerbated by the lack of security research focused on open-source ground stations, leaving the potential risks largely unexplored and insufficiently assessed. While some researchers have conducted conceptual studies on the security of common ground stations, these efforts have not extended to proposing practical security threats or conducting thorough evaluations to verify their findings. Furthermore, to the best of our knowledge, no previous research has addressed the cybersecurity of open-source ground stations such as SatNOGS and TinyGS. This highlights the urgent need for comprehensive research aimed at improving the security of open-source ground stations.
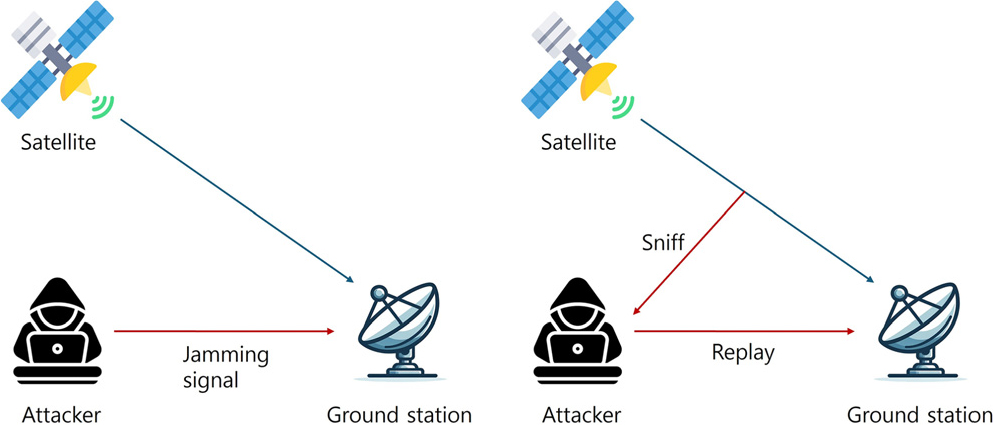
In this paper, we focus on evaluating the security of open-source ground stations by designing and testing realistic attack scenarios. The overview of our attack scenarios is shown in Fig. 1. Specifically, our research explores potential weaknesses within the RF communication layer, a critical area for the ground stations. To accomplish this, we first perform attack modeling to define the attacker’s objectives and capabilities. Based on these assumptions, we develop realistic RF attack scenarios, including jamming and replay attacks. These scenarios are then implemented and tested on an open-source ground station, TinyGS, to demonstrate their real-world applicability. Our experiments validate two RF attack scenarios on TinyGS to demonstrate that these attacks can be executed with minimal effort, highlighting the urgent need for improved security measures.
2. BACKGROUND
2.1. Open Source Ground Stations
The advent of open-source ground stations is transforming the landscape of satellite communication. These platforms, which rely on open-source software and hardware, are establishing a global network of ground stations that can track, receive, and decode signals from satellites, particularly those in low Earth orbit (LEO). This democratization is facilitating accessibility, cost-effectiveness, and collaboration in satellite communication.
2.1.1. SatNOGS
The SatNOGS [6] project is an open-source ground station software managed by the Libre Space Foundation [8]. The primary goal of this project is to establish a global network of satellite ground stations. The SatNOGS project provides users with easier access to satellite and ground station information and facilitates more efficient management of communication data. SatNOGS operates by having open-source contributors worldwide collecting satellite data through their ground stations and then transmitting this data to the centralized database. The transmitted data is accessible to all participants, and an interface for data verification is also provided.
2.1.2. TinyGS
TinyGS [7] is an open-source ground station software project that was initiated in 2019, originating from the ESP32 Fossa GroundStation. The project is based on LoRa boards and facilitates open-source satellite communication. TinyGS enables users to implement satellite communication at a low cost and to receive data from various satellites.
The TinyGS network enables users to obtain data indirectly. It integrates data sources shared by users worldwide, facilitating the collection and analysis of satellite data. This enhances the accessibility of satellite communication, creating an environment where anyone can access satellite data. The TinyGS project reduces the barriers to satellite communication and continues to evolve through contributions from the open-source community. This movement reduces the barriers to satellite communication and expands its potential applications in various fields.
2.2. RF Attacks
RF attacks are a type of RF network attack that exploits vulnerabilities inherent to wireless communication protocols with the objective of disrupting or manipulating data transmission. These attacks can target a wide range of wireless technologies, including Wi-Fi, Bluetooth, cellular networks, and satellite communications, and present a significant risk to both public safety and private enterprises.
2.2.1. Jamming
Jamming [9] is a deliberate blocking or interference with wireless communications. This is commonly performed by broadcasting a strong signal that overrides or obscures the target signal. The aim of this technique is to disrupt or prevent the exchange of information between devices or systems. It is often used for malicious purposes or in military operations to confuse enemy radar or communications. Jamming is a form of electronic interference that operates by transmitting radio signals at the same frequency signals as the target network or device. This results in a reduction of the signal-to-noise ratio, which makes it challenging or impossible for legitimate signals to be received.
2.2.2. Replay Attack
A replay attack [10] is a type of network attack whereby an attacker intercepts and retransmits data with the intention of gaining unauthorized access or disrupting communication. This attack involves capturing legitimate data packets or signals and then replaying them at a later time, thereby deceiving the system into accepting them as valid.
Replay attacks exploit the absence of authentication or novelty in communication protocols by intercepting authenticated data packets or signals during transmission, storing them for reuse, and then retransmitting the stored data at a later time, often to the same or a different recipient. This deception can result in the system or device accepting the replayed data as valid, thereby facilitating unauthorized access or disruption of communication.
3. THREAT MODEL
This section defines the attack vectors and establishes assumptions about the attacker’s objectives and abilities. Building on these assumptions, we develop practical attack scenarios.
3.1. Attack Model
3.1.1. Attack Vector
In this study, the attack vector is assumed to be the RF signal receiver of the ground station. The target ground station, G, is equipped with a receiver capable of receiving RF signals within a specific frequency band to collect satellite data. An attacker A can exploit this receiver of G by transmitting malicious RF signals. Other attack vectors, such as physical destruction or attacks via HTTP or MQTT channels, are considered beyond the scope of this paper.
3.1.2. Attacker’s Objectives
The attacker’s objectives are limited to Availability and Integrity attacks, which aim to disrupt the normal operation of a ground station or manipulate the packet data it receives. Confidentiality attacks are excluded from the scope of this research, as open-source ground station software is designed to publicly share all received packets on the web (Table 1).
TABLE 1.
Attacker’s objectives.3
By accomplishing these two objectives, an attacker can disrupt a ground station’s ability to receive valid packets. In addition, the attacker can make the ground station accept spoofed packets and send them to the server as legitimate data. Such attacks compromise not only the stability of the open-source ground station project but also the reliability of the shared packet data.
3.1.3. Attacker’s Capabilities
In this paper, the attacker is assumed to execute attacks based on RF signals, excluding other attack methods. The attacker is also assumed to have the ability to physically approach the target ground station to some extent and transmit signals using an appropriate transmitter. Additionally, the attacker is presumed to have knowledge of the satellite data that the target ground station intends to receive (Table 2).
TABLE 2.
Attacker’s capabilities
These capabilities are practical assumptions in the case of open-source ground stations. Since open-source ground stations typically do not handle highly confidential information and are often managed by individual contributors, physical access is relatively easy to achieve, making C1 a reasonable assumption. In addition, open-source ground station software provides public APIs where information about the frequencies and satellite signals collected by specific ground stations can be accessed. This makes C2 an easily achievable capability for an attacker.
3.2. Attack Scenario
Based on the attacker’s objectives and capabilities, we derive two attack scenarios: Jamming and Replay Attack.
3.2.1. Jamming
The jamming is designed to achieve objective O1 (Availability). The attacker, A, can physically approach the target ground station, G, according to capability C1, and has knowledge of the ground station’s center frequency due to capability C2. Using this information, the attacker transmits malicious RF signals at high signal power on the same center frequency as G, disrupting its ability to receive legitimate satellite signals.
3.2.2. Replay Attack
The replay attack aims to achieve objective O2 (Integrity). The attacker, A, uses capability C1 to physically access the target ground station, G, and capability C2 to determine which satellite, S, it is currently receiving signals from. By transmitting previously recorded signals from satellite S to G, the attacker tricks the ground station into recognizing outdated signals as real-time data, compromising the integrity of the received information.
4. METHODOLOGY
4.1. Jamming
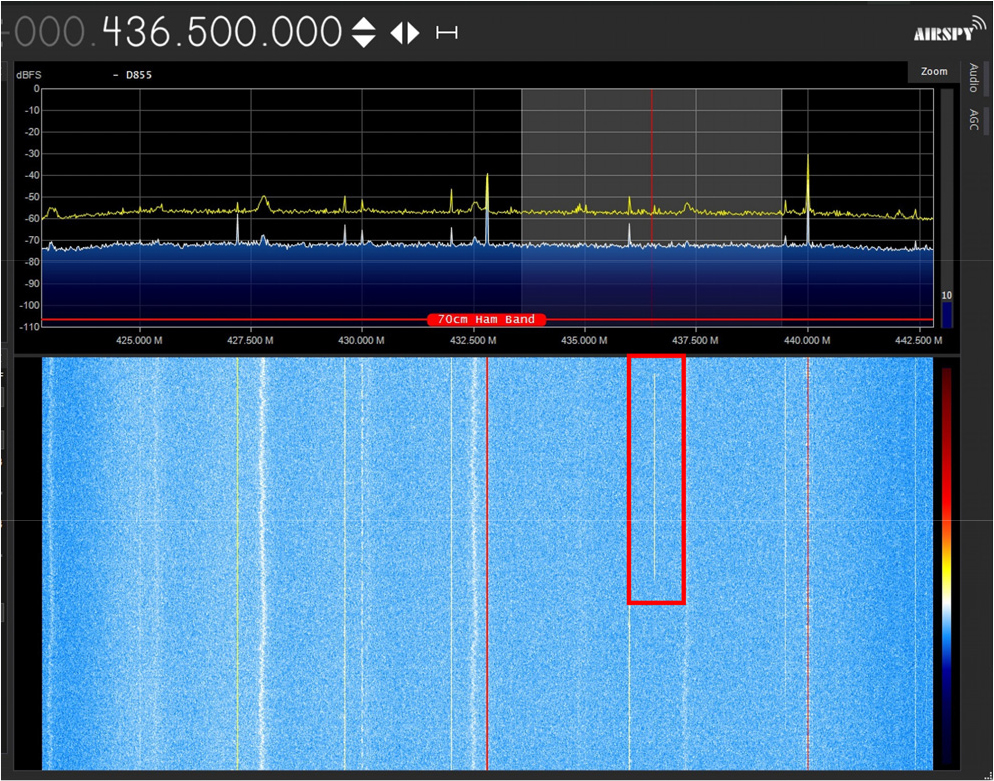
Our jamming method employed the use of a Software Defined Radio (SDR), the HackRF One, to generate interference signals that were targeted at satellite communication frequencies. A signal matching the specific frequency of the target satellite was first generated using GNU Radio.
The satellite’s overhead pass was then calculated in order to target the communication moment between the satellite and the ground station with precision. This approach ensures that the jamming is focused on the optimal communication timing, thereby maximizing its effectiveness.
The signal generation was precisely tuned within the satellite’s operational frequency. This interference signal represents a targeted method of potential communication disruption as satellites go public with their trajectory and frequencies.
4.2. Replay Attack
In contrast to the conventional ground-based replay attacks, our methodology has been devised to target satellite communication signals acquired during an actual satellite passage and the test packet from the ground station. By employing software-defined radio (SDR), it was possible to systematically capture broadcast signals from a satellite and ground station with an unknown protocol during its scheduled orbital pass. The captured signals comprise precise frequency and the complete communication packet.
The method diverged from traditional replay attack techniques, introducing a strategic signal retransmission protocol. The captured signal was transmitted during periods when the original satellite was not within the communication range. This approach permitted the simulation of potential interference scenarios in which there were no direct overlap of the signals.
An additional approach to the experiment is to transmit the signal during communication with a different satellite. By overlapping the signal transmission, it is possible to demonstrate the potential vulnerability of satellite communication systems to replay attacks.
5. EXPERIMENT
5.1. Environment
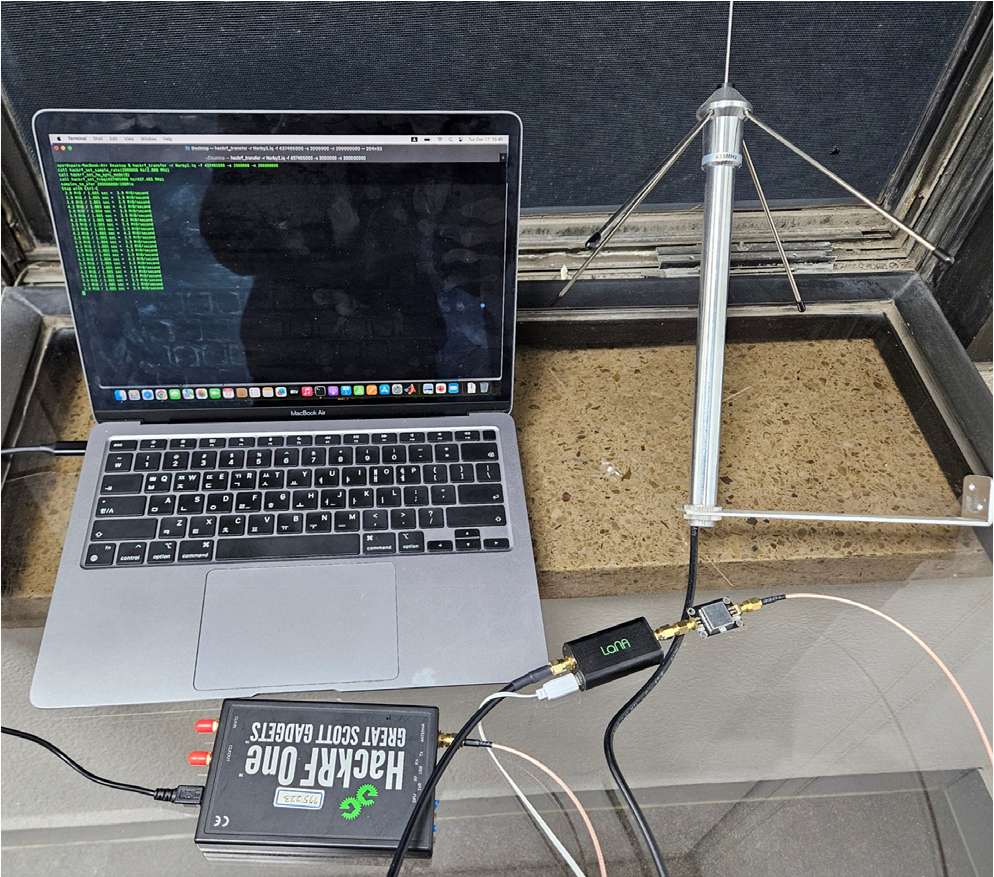
Our experimental setup can be seen in Fig. 2. The victim TinyGS ground station system is installed on LILYGO LoRa32 v2.1 board, a wireless LoRa module equipped with an ESP32 microcontroller, which is capable of supporting LoRa communication at frequencies of 433 MHz. A 433 MHz 3dbi omni antenna was utilized for the purpose of signal reception. To amplify and filter the signals, a Nooelec Lana LNA and a 433 MHz band pass filter is used. To simulate a satellite, TinyGS was set up on the same board using a default antenna. The generation and capturing of the signal are facilitated by HackRF One, a software-defined radio (SDR), used with a frequency range of 1 MHz to 6 GHz. The HackRF One was employed with a Z vertical antenna (VERT900) for jamming purposes and a 433 MHz 3dbi omni antenna for signal reception and replay.
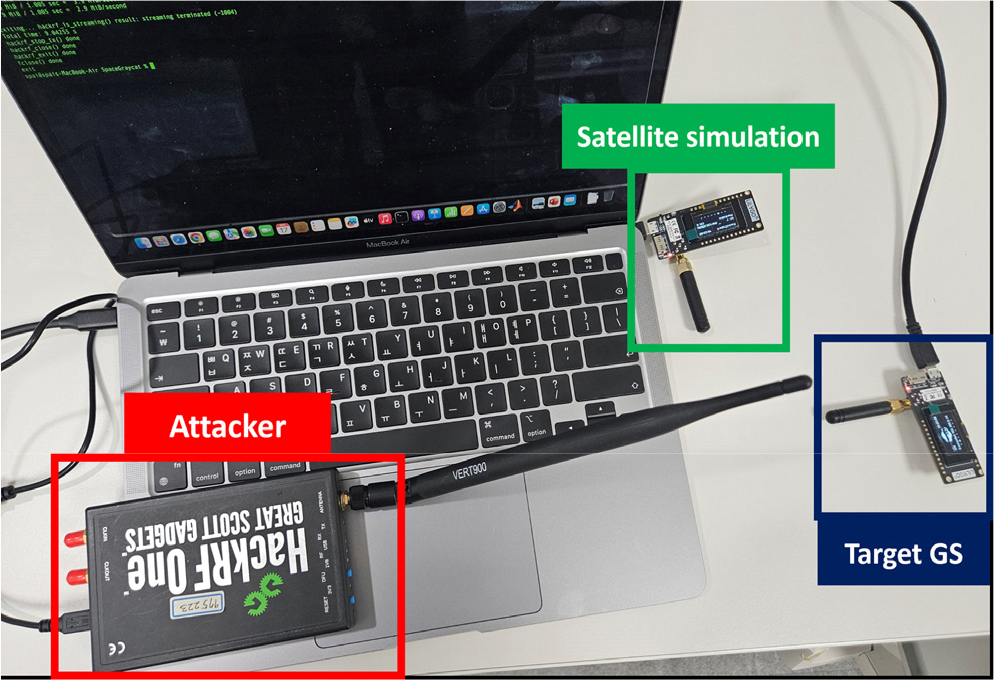
FIG. 2.
Experimental setup for jamming and replay attacks. The red box (Attacker) represents the transmitter performing the attack, while the blue box (Target GS) indicates the victim ground station. The green box (Satellite simulation) is used only in the jamming experiment to simulate a satellite by sending test packets. Note that some equipments and distances between devices differ from the actual environment.
5.2. Result
5.2.1. Jamming
The HackRF One was utilized to generate a jamming signal that precisely matched the specific frequency of the target satellite. The signal was then employed to interfere with the satellite’s downlink communication, effectively disrupting the signal and causing a reduction in signal quality.
During the transmission, the ground station was unable to receive signals from the satellite, thereby indicating that the communication link had been successfully disrupted. This was confirmed by an examination of the data displayed on the ground station’s control panel. The jamming signal was designed to be powerful enough to overpower the satellite’s downlink signal, thereby disrupting the communication link [11]. In this approach, the jamming signal was maintained at a fixed frequency. Subsequently, the jamming signal was terminated after a predetermined duration to ascertain whether communication could be established in the absence of jamming. This enabled us to observe the restoration of the satellite’s downlink signal and the ground station’s capacity to re-establish communication.
Once the jamming signal stopped, the ground station was able to receive signals from the satellite again, though with a slight delay. This delay occurred because the receiver needed time to recover from the jamming signal and reconnect to the satellite.
The experiment demonstrated the vulnerabilities inherent to satellite communication systems, particularly in LEO environments where satellites are more susceptible to jamming due to their proximity to Earth and the lower power of their signals. It emphasized the necessity of implementing robust anti-jamming measures, such as frequency hopping and adaptive detection algorithms, to preserve the integrity of the communication system against such attacks.
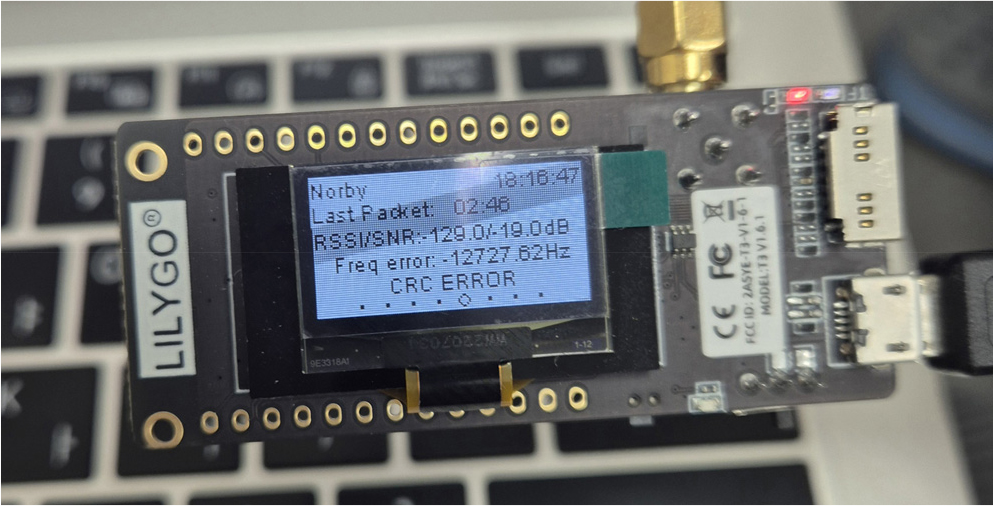
5.2.2. Replay Attack
Utilizing HackRF One, we successfully obtained the downlink communication signals from the Norby-2 satellite during its scheduled orbital pass. This process involved the precise capture of the frequency and the complete communication packet, including any authentication or encryption data (Fig. 3).
In the initial phase of the experiment, the ground station correctly identified the packet as originating from the satellite, even when the satellite was not within the field of view. This result indicated a potential vulnerability to replay attacks. Subsequently, when the signal was replayed during the pass of another satellite, the ground station initially accepted the packet, which demonstrated the feasibility of a replay attack.
By replaying the captured signal during the passage of another satellite, we could ascertain whether the ground station would erroneously accept the signal as an upcoming satellite, thereby verifying the possibility of a replay attack. We specifically targeted unknown protocols to examine how these might be exploited in a replay attack scenario.
6. CONCLUSION
In this paper, we evaluated the vulnerabilities of open-source ground stations. To this end, we designed and tested realistic attack scenarios, focusing on jamming and replay attacks. Our experiments demonstrate that replay attacks on unknown protocols are possible and presented the availability of jamming on ground stations.